Every day, millions of people receive emails claiming their bank account has been compromised, their package couldn’t be delivered, or they’ve won a prize. Most of these messages are phishing scams—sophisticated attempts by criminals to steal your personal information, passwords, and money.
This guide will help you understand how these scams work, recognize warning signs, and know what steps to take if you’ve been victimized.
What Are Phishing Scams and How Do They Work?
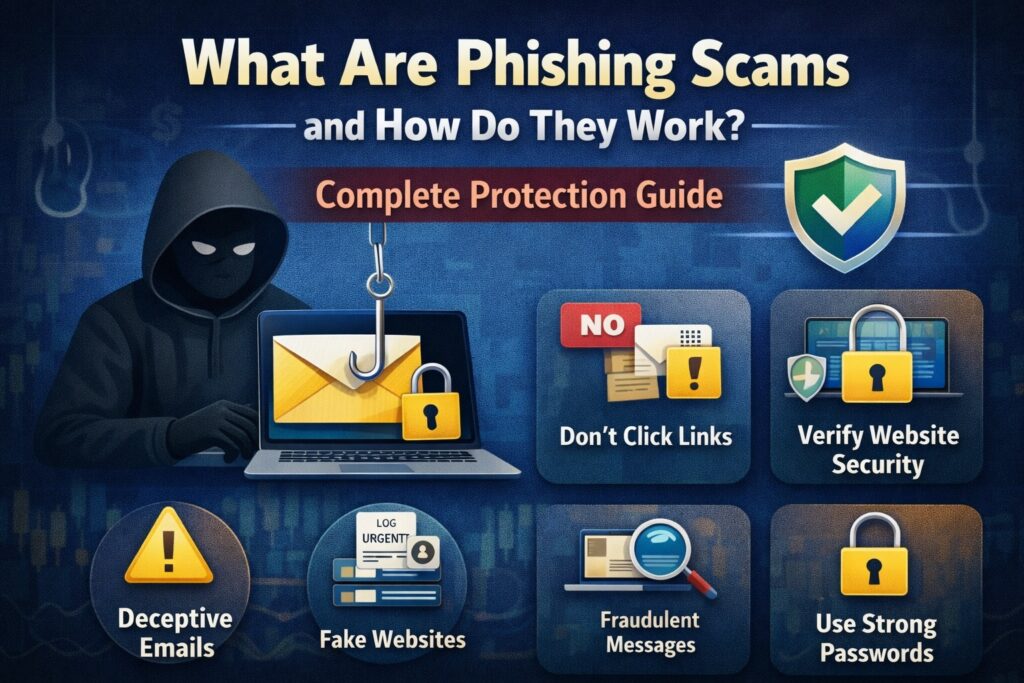
Phishing scams are cybercrimes where attackers impersonate legitimate organizations to trick you into revealing sensitive information. The term comes from “fishing”—scammers cast out bait hoping victims will bite.
Here’s how a typical attack unfolds:
The Setup: Criminals create fake emails, texts, websites, or phone scripts designed to look like they’re from trusted sources—your bank, a government agency, a delivery company, or even a coworker.
The Hook: The message contains urgent language: “Your account will be suspended,” “Suspicious activity detected,” or “Immediate action required.” This urgency pressures you to act without thinking.
The Trap: You’re directed to click a link, download an attachment, call a phone number, or reply with personal information. These actions lead to fake websites that steal your credentials, malware that infects your device, or phone conversations where scammers extract information.
The Theft: Once scammers have your information, they can access your bank accounts, make unauthorized purchases, steal your identity, or sell your information to other criminals.
Common Types of Phishing Scams to Watch Out For
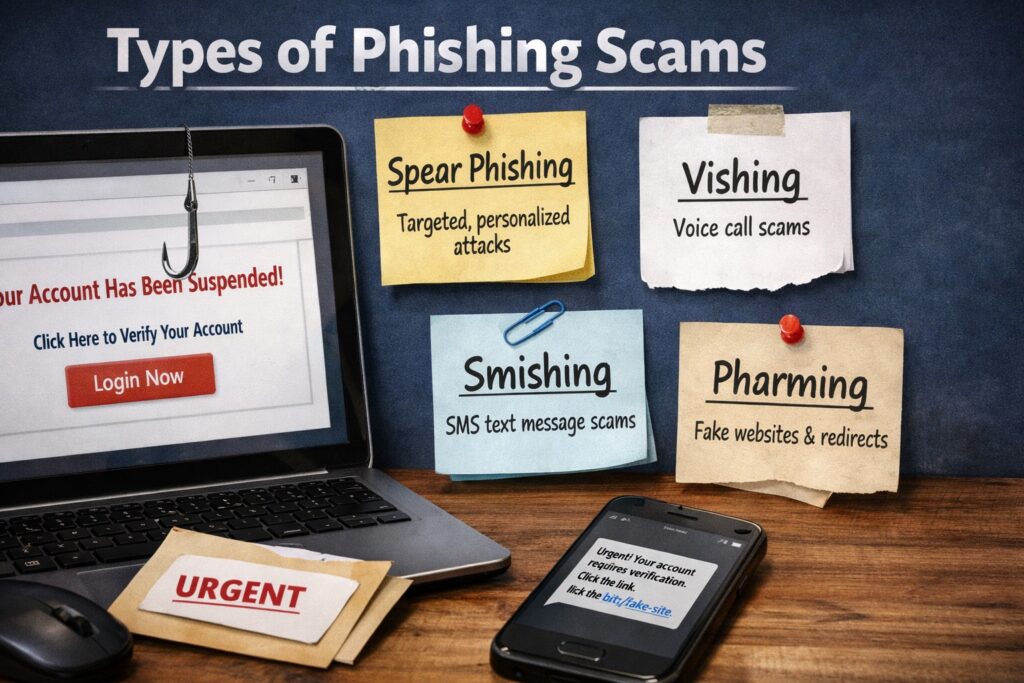
1. Email Phishing Scams
Email phishing scams are the most common form. Attackers send mass emails appearing to come from legitimate organizations, using official-looking logos and urgent warnings about account problems.
Phishing scam examples:
- “Your Amazon account has been locked”
- “Unusual sign-in attempt detected”
- “Your package could not be delivered”
- Fake bank phishing emails claiming fraudulent charges
How to spot a phishing email? Look for generic greetings (“Dear Customer”), sender addresses that don’t match the company’s domain, and requests for immediate action.
2. Smishing Scams (SMS Phishing)
Smishing scams use text messages to reach victims. These SMS phishing scams exploit mobile trust and make link verification harder.
Common tactics: Fake delivery notifications, bank security alerts, prize notifications, or fake customer service messages asking you to call back.
3. Vishing Scams (Voice Phishing)
Vishing scams involve phone calls where criminals impersonate banks, the IRS, tech support, or law enforcement. The key difference between phishing and vishing is that phishing uses digital messages while vishing uses voice communication.
Scammers create urgency through threats of legal action, account closure, or security breaches, requesting sensitive information or immediate payment.
4. Spear Phishing
Spear phishing targets specific individuals using researched personal information. Attackers gather details from social media and public records to create highly personalized, believable messages.
Example: An email appearing from your CEO asking you to urgently process a wire transfer, mentioning a project you’re actually working on.
5. Clone Phishing
Clone phishing involves copying a legitimate email you received and replacing links with malicious versions. Since you recognize the original message, you’re more likely to trust the clone.
6. Business Email Compromise Scams
Business email compromise scams target companies by impersonating executives or vendors, potentially resulting in fraudulent wire transfers worth hundreds of thousands of dollars.
Top Signs You’re Being Targeted by a Phishing Scam
Recognizing phishing scam warning signs is your first defense:
Signs of a Phishing Email
- Unexpected Messages: Emails, texts, or calls you weren’t expecting, requesting action or information
- Generic Greetings: “Dear Customer” instead of your actual name
- Urgent Language: “Act now,” “Your account will be closed,” or “Immediate action required”
- Suspicious Email Addresses: Sender doesn’t match the organization’s official domain, with subtle misspellings
- Mismatched Links: Hover over links—if the URL contains misspellings or doesn’t match the claimed destination, it’s likely a phishing link
- Unexpected Attachments: Legitimate companies rarely send unexpected executable files or compressed attachments
- Grammar Errors: Many attempts contain awkward phrasing or spelling mistakes
- Requests for Sensitive Information: Legitimate organizations never ask for passwords, Social Security numbers, or credit card details via email or unsolicited calls
- Too-Good-To-Be-True Offers: Prize notifications, inheritances from unknown relatives, or guaranteed investment returns
- Pressure to Act: Artificial urgency preventing careful verification
How Hackers Steal Passwords Using Phishing
Understanding credential theft scams reveals why phishing is so effective:
Fake Login Pages: The most common method involves fake login phishing pages. These phishing websites look nearly identical to legitimate login pages. You receive an email about an account problem, click the link, enter your credentials on a fake page, and scammers capture your information.
Protection tip: Never click links in emails to log into sensitive accounts. Type the website address directly into your browser.
Keylogging Malware: Some attacks install malware that records everything you type, capturing passwords and credit card numbers without your knowledge.
Session Hijacking: Advanced attacks steal “session cookies” that keep you logged in, allowing criminals to access accounts even without your password.
Tips for Avoiding Phishing Scams
Implementing phishing scam prevention strategies reduces your risk:
Phishing Prevention Techniques
1. Verify Before You Trust: Call organizations using official numbers from their website, not numbers in messages. Type URLs directly rather than clicking links.
2. Use Two-Factor Authentication: Two-factor authentication phishing protection adds critical security. Even if scammers steal your password, they can’t access your account without the second factor.
3. Keep Software Updated: Regular updates patch security vulnerabilities. Enable automatic updates for operating systems, browsers, antivirus software, and applications.
4. Use Security Software: Quality antivirus software can detect phishing websites, warn about suspicious links, scan emails, and remove malware.
5. Think Before You Click: Pause before clicking links or providing information. Ask: Was I expecting this? Does it make sense? Can I verify this independently?
6. Check URLs Carefully: Verify HTTPS and the padlock icon, examine URLs for misspellings, and be suspicious of shortened URLs.
7. Be Cautious on Public Wi-Fi: Avoid accessing sensitive accounts on public networks or use a VPN.
8. Limit Personal Information Sharing: Review privacy settings on social media and limit what you share publicly to make spear phishing harder.
9. Trust Your Instincts: If something feels off, verify rather than risk becoming a victim.
What to Do After Clicking a Phishing Link
If you’ve clicked a phishing link or provided information, take immediate action:
Steps to Take After Phishing Fraud
Immediate Actions:
- Disconnect from Internet: Stop malware from spreading or communicating with scammers
- Change Passwords: Update credentials for affected accounts from a secure device
- Run Security Scans: Use updated antivirus software to scan for malware
- Enable Two-Factor Authentication: Activate on all important accounts immediately
Short-Term Actions:
5. Monitor Accounts: Check for unauthorized transactions and set up activity alerts
6. Contact Financial Institutions: Alert banks and credit card companies about potential compromise
7. Check for Unauthorized Access: Review account logs for suspicious logins or changes
8. Report the Attack: Report phishing scam incidents to help protect others
Long-Term Actions:
9. Place Fraud Alerts: Consider fraud alerts on credit reports with major bureaus
10. Monitor Your Credit: Regularly check for unauthorized accounts or inquiries
How to Report Phishing Scams
Reporting helps authorities track operations. Here’s how to report phishing scam incidents:
United States: FTC (reportfraud.ftc.gov), FBI IC3 (ic3.gov), Anti-Phishing Working Group (reportphishing@apwg.org)
United Kingdom: Action Fraud (actionfraud.police.uk), National Cyber Security Centre (report@phishing.gov.uk)
India: Cybercrime Portal (cybercrime.gov.in), local cyber police stations
Email Providers: Gmail, Outlook, and Yahoo all have “Report phishing” options in their interfaces
Report to Impersonated Organizations: Forward phishing emails to the organization being impersonated (most banks have dedicated phishing@bankname.com addresses)
Professional Help: If you’ve lost money to phishing fraud, truclaim.tech specializes in helping victims by investigating fraud, tracing funds, coordinating with financial institutions, working with law enforcement, and providing recovery guidance.
Phishing Scam Recovery: Can You Get Your Money Back?
Recovery depends on how quickly you act. Here’s what you need to know about phishing scam recovery:
How to Recover from Phishing Attack
Financial Recovery Steps:
- Contact Your Bank Immediately: Banks often have fraud protection. If you report unauthorized transactions quickly (within 60 days), you may not be liable.
- Request Chargebacks: Credit cards can reverse fraudulent transactions. Provide all documentation when filing disputes.
- Work with Payment Services: PayPal, Venmo, and similar services have fraud reporting systems. Report immediately through official channels.
Professional Recovery: Phishing scam recovery services financial platforms can help by tracking stolen funds, negotiating with banks, coordinating with law enforcement, and providing fraud victim support resources.
Important: Be cautious of “recovery scams” claiming they can retrieve your money for upfront fees. Legitimate services are transparent and don’t guarantee outcomes.
Related Scams and Cross-Platform Threats
Phishing often overlaps with other fraud:
Cryptocurrency: Phishing steals crypto by directing victims to fake login pages for exchanges. Report crypto scam online incidents to help authorities.
Forex Trading: Forex fraud situations often begin with phishing-style offers. Report forex scam operations to financial regulatory bodies.
Bitcoin: Bitcoin scams use phishing to steal wallet credentials. Avoid bitcoin investment scams by verifying platforms before depositing funds.
Investment Fraud: To report investment scam operations using phishing, contact the SEC, FCA, or your country’s financial regulator.
Support Resources: Fraud victim support services provide emotional support, reporting guidance, legal assistance connections, and community support. Report scammer online through truclaim.tech for comprehensive fraud documentation and recovery assistance.
Final Thoughts: Staying Safe in a Phishing World
Phishing scams represent one of the most persistent cybersecurity threats. Understanding how to identify phishing scams, recognizing phishing scam warning signs, and knowing what to do if targeted are essential skills for anyone online.
Key protective principles:
- Verify unexpected requests through independent channels
- Never click links in unsolicited messages
- Use two-factor authentication on important accounts
- Keep software and security tools updated
- Think before acting on urgent requests
- Trust your instincts when something feels wrong
If you’ve fallen victim to phishing fraud, don’t let embarrassment prevent seeking help. These sophisticated crimes fool people at all expertise levels. Acting quickly increases recovery chances and prevents further damage.
Visit Tru Claim immediately if you’ve been affected by phishing attacks, lost money to online fraud, or need guidance on reporting and recovery. Our team specializes in investigating phishing cybercrime, tracking stolen funds, and coordinating with financial institutions and authorities to pursue all available recovery options.
Contact us, and our team investigates online financial scams, tracks cryptocurrency transactions, and helps victims get their money back.
Stay informed about phishing scam prevention, maintain healthy skepticism toward unexpected communications, and follow security best practices to protect yourself online. Stay alert, stay skeptical, and verify through official channels before taking action.
For more updates, follow us on: