The Growing Threat of Cryptocurrency Scams

Cryptocurrency has fundamentally transformed the global financial landscape, creating unprecedented opportunities for trading, investing, and transferring money across borders. Digital currencies, such as Bitcoin, Ethereum, and thousands of altcoins, have democratized access to financial markets and introduced innovative blockchain technologies. However, this revolutionary space has also become a fertile hunting ground for sophisticated fraudsters who exploit the complexity, anonymity, and irreversible nature of cryptocurrency transactions.
Cryptocurrency scams have evolved into a multi-billion-dollar criminal industry, targeting everyone from novice investors to experienced traders. Understanding how to identify cryptocurrency scams and implementing strong protection strategies is now essential for anyone participating in the digital asset ecosystem.
The growing threat stems from several factors: the relative anonymity of blockchain transactions, the lack of comprehensive regulation in many jurisdictions, the irreversible nature of crypto transfers, and the technical complexity that intimidates many users. Scammers exploit these characteristics, knowing that once they obtain your digital assets or private keys, recovery becomes nearly impossible without professional intervention.
This comprehensive guide explores the most common types of fraud targeting crypto investors, including crypto bitcoin scams and altcoin fraud, provides actionable protection tips, reveals warning signs to watch for, and explains what to do if you’ve been victimized. Whether you’re a seasoned crypto investor or just beginning your journey into digital assets, this knowledge could save you from devastating financial losses.
What Are Cryptocurrency Scams?
Cryptocurrency scams are fraudulent schemes designed to illegally obtain someone’s digital assets, private keys, wallet credentials, or personal information through deception, manipulation, or technical exploitation. These scams range from simple phishing emails to sophisticated operations that involve months of relationship-building before the financial theft occurs.
Unlike traditional financial fraud, cryptocurrency transactions present unique challenges for victims:
- Irreversibility: Once a crypto transaction is confirmed on the blockchain, it cannot be reversed or canceled. There’s no bank to call for a chargeback, no credit card company to dispute the transaction with, and no central authority to intervene.
- Anonymity: While blockchain transactions are publicly recorded, the identities behind wallet addresses often remain anonymous or pseudonymous, making it difficult to trace and prosecute scammers.
- Lack of Regulation: Many cryptocurrency platforms operate in regulatory gray areas or jurisdictions with limited consumer protection, leaving victims with few legal recourses.
- Technical Complexity: The technical nature of cryptocurrencies intimidates many users, creating information asymmetry that scammers exploit by using confusing jargon and complex explanations.
Understanding these fundamental characteristics helps explain why protecting yourself in the crypto space requires a different approach than traditional financial security.
What Are the Most Common Crypto Scam Types?

Let’s explore the most prevalent scams that pose the greatest risk to digital asset holders, along with warning signs and protection strategies.
1. Cryptocurrency Investment Scams
Cryptocurrency investment scams represent the most financially devastating category of fraud in the digital asset space. These sophisticated operations promise extraordinary returns with minimal risk, exploiting people’s desire for financial freedom and fear of missing out on the next big opportunity.
How These Scams Operate?
Fraudsters create convincing platforms that mimic legitimate trading or staking services. These platforms feature professional websites, fake testimonials, fabricated trading charts, and impressive dashboards showing fictitious profit growth. Some even allow small initial withdrawals to build trust before requesting larger deposits.
Warning Signs to Watch For:
- Guaranteed returns or “risk-free” profit promises
- Pressure to invest quickly before missing “exclusive opportunities”
- Unrealistic profit percentages (20-50% monthly returns)
- Difficulty withdrawing funds or increasingly complex withdrawal requirements
- Lack of verifiable business registration or regulatory oversight
- Anonymous or untraceable team members
Protection Strategies:
Before investing in any crypto platform, research extensively. Verify the company’s registration, check for regulatory compliance, read independent reviews, and test small withdrawals before committing significant funds. Remember: legitimate platforms are transparent about risks and never guarantee specific returns in volatile markets. Many of these forex scam warning signs also apply to crypto investment platforms.
2. Fake Crypto Apps
Fake crypto apps have infiltrated both official and third-party app stores, appearing remarkably similar to legitimate cryptocurrency wallets and exchanges. These malicious applications are particularly dangerous because they often look professionally designed and may even appear in search results above authentic apps.
How These Apps Steal Your Information?
Once installed, fake apps employ various techniques to steal credentials:
- Keylogging software captures everything you type, including passwords and seed phrases
- Screen recording monitors your activities
- Direct wallet access steals funds immediately upon login
- Clipboard hijacking replaces copied wallet addresses with the scammer’s address
How to Protect Your Crypto Wallet?
Always download cryptocurrency apps directly from official websites, verify the developer’s identity, read recent user reviews carefully, check the app’s permission requests, and enable two-factor authentication whenever possible. Consider using hardware wallets for significant holdings.
3. Fake Crypto Websites
Fake crypto websites employ sophisticated phishing techniques to impersonate authentic exchanges, wallets, and DeFi platforms. These sites are designed to harvest login credentials, seed phrases, and private keys.
Red Flags to Watch For:
- Slight misspellings in domain names (e.g., “binannce.com” instead of “binance.com”)
- Missing HTTPS encryption or invalid security certificates
- Poorly written content with grammatical errors
- Unsolicited emails or social media messages linking to the site
- Requests for seed phrases or private keys (legitimate platforms NEVER ask for these)
- Urgent prompts to “verify your account” or “claim rewards”
Protection Tips:
Always manually type exchange URLs into your browser, bookmark legitimate sites for easy access, verify SSL certificates, never click links in unsolicited messages, and consider using a dedicated device for crypto transactions.
4. Fraudulent Initial Coin Offerings (ICOs)
Fake ICO scams promise investors early access to revolutionary blockchain projects with guaranteed massive returns. These scams became especially prevalent during the 2017-2018 ICO boom and continue today with newer variations like Initial DEX Offerings (IDOs) and token presales.
How to Spot a Scam Before Investing?
Legitimate ICO projects have transparent teams with verifiable identities, detailed technical white papers, clear token utility and economics, realistic roadmaps, working prototypes or MVPs, active community engagement, and smart contract audits from reputable firms.
Warning Signs:
- Anonymous team members or fake LinkedIn profiles
- Plagiarized white papers
- Unrealistic promises (“guaranteed 100x returns”)
- Pressure to invest before the token launch
- No working product or testable demo
- Vague or missing technical documentation
Before investing in any ICO or token sale, research the team’s background, verify their previous projects, analyze the token economics, check for third-party audits, and assess whether the blockchain solution actually solves a real problem.
5. Cloud Mining Scams
Cloud mining scams promise passive income through the rental of remote mining hardware. These platforms claim you can earn daily or monthly returns from cryptocurrency mining without purchasing, maintaining, or powering expensive equipment.
How the Fraud Works?
Scammers create professional websites showing mining dashboards with fabricated statistics. They may even pay out small initial returns to build credibility. However, most don’t own any actual mining equipment and simply operate as Ponzi schemes, using new investor deposits to pay earlier participants until the scheme collapses.
Verification Steps:
Legitimate cloud mining requires substantial infrastructure. Before investing, demand verifiable proof of mining operations (facility photos, mining pool statistics, blockchain records of mined coins), research the company’s registration and history, calculate realistic profitability considering electricity costs and difficulty increases, and compare offerings against industry standards.
6. Blackmail and Extortion Scams
Blackmail scams leverage fear and embarrassment to extract cryptocurrency payments. Scammers send emails claiming to have compromising information, such as:
- Webcam recordings of you visiting adult websites
- Hacked email or social media accounts
- Stolen personal photos or documents
- Evidence of illegal activity
These scams often include personal information (like an old password obtained from data breaches) to appear credible and increase panic.
What to Do:
Never pay blackmail demands. These are almost always bluffs with no actual compromising material. Instead, change your passwords immediately, enable two-factor authentication on all accounts, run malware scans, report the extortion to law enforcement, and document all communications. Services like truclaim.tech can help you understand your options and report these incidents properly.
7. Pump and Dump Schemes
Pump and dump schemes involve coordinated efforts to artificially inflate a low-value cryptocurrency’s price through misleading promotion, then selling holdings at the peak, leaving later investors with worthless tokens.
How These Scams Operate?
Scammers accumulate large quantities of obscure, low-market-cap cryptocurrencies, then aggressively promote them through social media, Telegram groups, Discord servers, and influencer endorsements. They create FOMO (fear of missing out) by claiming “insider information” or “imminent major announcements.”
Once enough retail investors buy in and the price spikes, the scammers dump their holdings, crashing the price and leaving victims with massive losses.
Protection Strategies:
Be extremely skeptical of cryptocurrency recommendations from unknown sources, avoid making investment decisions based on social media hype, research any cryptocurrency thoroughly before purchasing, analyze trading volume and market cap sustainability, and never invest based solely on fear of missing out.
8. Phishing Scams
Phishing scams remain among the most prevalent threats in the crypto space. These attacks involve fraudsters impersonating legitimate companies, exchanges, or services to steal credentials and funds.
Common Phishing Techniques:
- Email Phishing: Messages appearing to be from exchanges about security issues, account verification, or suspicious activity
- SMS Phishing (Smishing): Text messages claiming urgent account problems
- Social Media Phishing: Direct messages from fake customer support accounts
- Malicious Attachments: Documents or files containing keyloggers or malware
Protection Tips:
Recognize signs of a phishing email by verifying sender addresses carefully (scammers use similar-looking email addresses), never click links in unsolicited messages, manually navigate to websites by typing URLs, hover over links to preview actual destinations, be suspicious of urgent or threatening language, verify customer support contacts through official websites, and never share seed phrases or private keys with anyone, regardless of who claims to need them.
9. Ponzi and Pyramid Schemes
Ponzi and pyramid schemes promise high returns but generate profits solely from new investor deposits rather than legitimate business activities.
Ponzi Schemes pay returns to earlier investors using capital from newer investors, creating an illusion of profitability until the scheme collapses when recruitment slows, or withdrawal demands exceed new deposits.
Pyramid Schemes require participants to recruit others, with income derived primarily from recruitment fees rather than actual product sales or crypto trading.
Red Flags:
- Emphasis on recruiting new members
- Complex compensation structures
- Guaranteed high returns regardless of market conditions
- Difficulty withdrawing funds
- Lack of verifiable trading or business activity
10. Rug Pull Scams
A rug pull occurs when developers create a new cryptocurrency or DeFi project, attract significant investment, then suddenly abandon the project and drain the liquidity pool, leaving investors with worthless tokens.
Types of Rug Pulls:
- Liquidity Stealing: Developers remove all liquidity from decentralized exchanges
- Limiting Sell Orders: Smart contracts prevent investors from selling tokens
- Dumping Developer Tokens: Team members sell massive pre-mined holdings, crashing the price
Warning Signs:
- Anonymous development teams
- Unaudited smart contracts
- Concentrated token holdings (large percentages held by a few wallets)
- Locked liquidity for short periods only
- Aggressive marketing without substantial product development
11. Pig Butchering Scams
Pig butchering represents one of the most sophisticated and emotionally devastating scams in cryptocurrency. These long-term operations involve building romantic or friendship relationships with victims over weeks or months before introducing fraudulent investment opportunities.
How the Scam Works?
Scammers contact victims through dating apps, social media, or messaging platforms. They invest significant time building trust and emotional connections. Eventually, they introduce cryptocurrency investment opportunities, often demonstrating their own “successful” trading on fake platforms. They encourage victims to start with small investments, show fake profits to build confidence, then pressure for increasingly large deposits before disappearing with all funds.
Protection:
Be extremely cautious of online contacts who discuss cryptocurrency investments, especially those you’ve never met in person. Verify investment platforms independently, never invest based solely on someone else’s recommendation, and consult with trusted financial or friends advisors before making significant commitments.
Learn to recognize signs of online dating scams early: anyone who quickly professes love and then mentions investment opportunities is likely a scammer.
12. NFT Scams
While NFTs (Non-Fungible Tokens) offer legitimate use cases, they’ve also become vehicles for fraud:
- Fake NFT Marketplaces: Phishing sites mimicking OpenSea or other platforms
- Counterfeit NFTs: Stolen artwork minted as NFTs by scammers
- Pump and Dump NFT Projects: Artificial hype followed by price crashes
- Rug Pull NFT Collections: Projects that disappear after initial sales
How Cryptocurrency Scams Are Evolving?
Cryptocurrency scams continue to evolve, reflecting an ongoing arms race between security measures and criminal innovation. Modern scammers employ:
Advanced Social Engineering: Elaborate backstories, professional personas, and psychological manipulation techniques that exploit trust, fear, greed, and urgency.
AI-Generated Content: Deepfake videos of celebrities endorsing scams, AI-written white papers, and chatbots that convincingly impersonate customer support.
Cross-Platform Operations: Coordinated campaigns across Telegram, Discord, Twitter, Instagram, and WhatsApp to appear legitimate and build community trust.
Regulatory Arbitrage: Operating from jurisdictions with weak crypto regulations while targeting victims in countries with limited cross-border enforcement capabilities.
DeFi Exploitation: Exploiting the permissionless nature of decentralized finance to create sophisticated scams involving yield farming, liquidity pools, and governance tokens.
Tips for Avoiding Cryptocurrency Scams
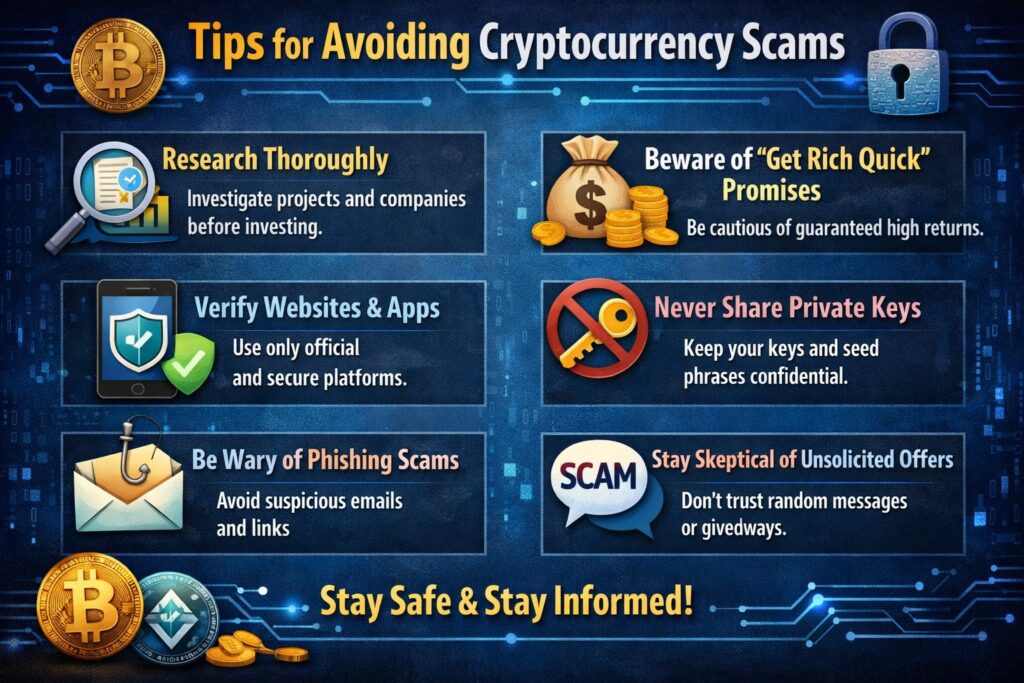
Implementing comprehensive crypto scam protection strategies safeguards your digital assets:
1. Verify Before Trust
Always verify platform legitimacy through independent research, regulatory databases, and community feedback before investing or sharing information.
2. Secure Your Crypto Properly
- Use hardware wallets for significant holdings
- Enable two-factor authentication on all accounts
- Store seed phrases offline in secure locations
- Never share private keys with anyone
- Regularly update wallet software and security protocols
3. Recognize Warning Signs
- Guaranteed returns or risk-free profits
- Pressure to invest quickly
- Unsolicited investment opportunities
- Requests for private keys or seed phrases
- Anonymous team members
- Lack of regulatory compliance
4. Conduct Due Diligence
Before investing in any cryptocurrency project:
- Research team backgrounds and verify identities
- Review white papers for technical viability
- Check smart contract audits from reputable firms
- Analyze tokenomics and distribution
- Assess real-world problem-solving potential
- Review community sentiment across independent platforms
5. Start Small and Test Withdrawals
Before committing significant funds to any platform, test small deposits and withdrawals to verify functionality and legitimacy.
6. Educate Yourself Continuously
The crypto space evolves rapidly. Stay informed about new scam tactics, security best practices, and regulatory developments through reputable sources.
7. Use Security Tools
Implement protection through:
- VPN services for privacy
- Anti-phishing browser extensions
- Dedicated devices for crypto transactions
- Email filters to block suspicious messages
- Wallet address whitelisting
What to Do If You Lost Crypto to a Scam
If you’ve become a victim, immediate action is critical:
Step 1: Document Everything
Preserve all evidence, including:
- Transaction hashes and blockchain records
- Screenshots of conversations and websites
- Wallet addresses involved
- Dates, times, and amounts
- Marketing materials and promises made
Step 2: Report the Scam
Take these reporting steps:
- Local Law Enforcement: File a police report for official documentation
- Federal Agencies: Contact the FBI’s Internet Crime Complaint Center (IC3), FTC, or SEC
- Exchange Platforms: Report scam addresses to exchanges to potentially freeze funds
- Blockchain Analysis: Some platforms can flag suspicious addresses
- Consumer Protection: File complaints with relevant consumer protection agencies
- Online Reporting Platforms: Report financial scam online through dedicated platforms like truclaim.tech that specialize in crypto fraud
Step 3: Seek Professional Help
Professional crypto scam recovery services can provide crucial assistance. Specialists can help with:
- Tracing transactions across multiple wallets and exchanges
- Navigating complex international jurisdictions
- Working with exchanges, law enforcement, and legal systems
- Employing recovery strategies and legal remedies
Truclaim.tech specializes in helping cryptocurrency scam victims navigate the recovery process. Their team investigates digital asset fraud, tracks cryptocurrency transactions across blockchain networks, coordinates with exchanges and authorities, and works to recover stolen funds. If you’ve lost digital assets to fraudulent platforms, fake apps, or investment scams, truclaim.tech can provide expert guidance and support.
Step 4: Secure Your Remaining Assets
After a scam:
- Change all passwords immediately
- Enable enhanced security features
- Move remaining crypto to new, secure wallets
- Monitor accounts for suspicious activity
- Consider professional security audits
Step 5: Warn Others
Share your experience (while protecting personal details) to help others avoid similar scams. Report scam websites and social media accounts to platforms and warn community members about specific tactics used against you.
Building Long-Term Crypto Security
Effective protection requires ongoing vigilance and comprehensive security practices:
Technical Security Measures
Hardware Wallets: Store significant cryptocurrency holdings on hardware wallets disconnected from the internet. Popular options include Ledger and Trezor devices that keep private keys offline.
Multi-Signature Wallets: Require multiple approvals for transactions, preventing single points of failure.
Regular Security Audits: Periodically review security settings, connected applications, and authorized devices.
Wallet Security Best Practices:
- Use unique, complex passwords for each platform
- Implement two-factor authentication everywhere possible
- Regularly update wallet software
- Verify smart contract permissions
- Use address whitelisting for known recipients
Behavioral Security Practices
Skepticism as Default: Approach all cryptocurrency opportunities with healthy skepticism, especially those promising extraordinary returns.
Independent Verification: Never rely solely on information provided by the party requesting your investment. Independently verify all claims through multiple sources.
Community Consultation: Engage with knowledgeable community members and seek second opinions on suspicious opportunities.
Continuous Learning: Stay updated on emerging scam tactics and protection strategies through reputable cryptocurrency security resources.
The Future of Cryptocurrency Fraud Prevention
As the cryptocurrency industry matures, fraud prevention is improving through:
Enhanced Regulation: Governments worldwide are implementing clearer regulatory frameworks that provide consumer protections while fostering innovation.
Blockchain Analytics: Advanced tools can track cryptocurrency movements, identify suspicious patterns, and potentially freeze scammer funds.
Exchange Cooperation: Major exchanges increasingly cooperate to block known scam addresses and share threat intelligence.
Educational Initiatives: Industry organizations and platforms are investing in user education about security and scam recognition.
AI-Powered Detection: Machine learning algorithms can identify phishing attempts, fake websites, and suspicious transaction patterns in real-time.
Protecting Your Digital Assets with Truclaim
The cryptocurrency revolution offers unprecedented financial opportunities, but it also demands unprecedented personal responsibility for security. Understanding how to identify scams, recognizing warning signs, and implementing comprehensive protection strategies are essential skills for every digital asset holder.
Remember these fundamental principles:
- Verify everything independently before investing or sharing information
- Protect your private keys as if they were the keys to your bank vault—because they are
- Be skeptical of guarantees in a volatile market where nothing is certain
- Start small and test before committing significant funds
- Stay informed about evolving scam tactics and security best practices
- Seek help immediately if you suspect you’ve been scammed
The threat of cryptocurrency scams is real, but with knowledge, vigilance, and proper security practices, you can navigate the digital asset ecosystem safely. Common scams share identifiable patterns, and by familiarizing yourself with these fraud types, you become a much harder target.
If you’ve already fallen victim to cryptocurrency fraud, don’t lose hope. While recovery is challenging, professional services like truclaim.tech specialize in investigating digital asset fraud, tracking blockchain transactions, and working to recover stolen funds. Their expertise in blockchain analysis and coordination with exchanges and authorities provides victims with the best possible chance of recovery.
Remember: legitimate cryptocurrency platforms and services will never pressure you, guarantee returns, request your private keys, or rush you into decisions. When in doubt, step back, research thoroughly, and consult with trusted experts.
If you’ve been affected by any cryptocurrency scam or suspect you’re being targeted, visit truclaim.tech immediately for expert investigation services, recovery assistance, and guidance on reporting fraud effectively. Don’t face crypto fraud alone—professional help is available.
Contact us, and our team investigates online financial scams, tracks cryptocurrency transactions, and helps victims get their money back.
Stay safe, stay skeptical, and protect your digital assets with the seriousness they deserve.
For more updates, follow us on: